Business
Infosec products of the month: June 2023
Published
2 years agoon
By
GFiuui45fg
Here’s a look at the most interesting products from the past month, featuring releases from: 1Password, Bitdefender, Cequence Security, ConnectSecure, Cymulate, Cytracom, Datadog, Delinea, Edgescan, Enveedo, ESET, Index Engines, Island, iStorage, Lacework, NetApp, Netscout, Netskope, NinjaOne, Okta, Permit.io, PingSafe, Quantinuum, Seceon, and Zilla Security.
Island integrates DLP capabilities for ChatGPT, Bard, and other AI
Island announced an enterprise-grade set of Data Loss Prevention (DLP) capabilities for all popular interactive AI-type applications including ChatGPT, Bard and others, within its Enterprise Browser. These features are available in multiple deployment modes to accommodate various interaction types; integrated into the browser itself, managing AI extensions; and as a standalone desktop application, delivering the industry’s broadest set of protections for this rapidly growing category of productivity products.


Permit.io launches FoAz to give frontend developers the keys to security
Short for frontend-only authorization, FoAz is a technology that empowers frontend developers to use sensitive APIs directly from the frontend, without requiring any backend code, while maintaining the highest level of security.


Bitdefender GravityZone Security for Mobile provides protection against mobile attack vectors
Leveraging Bitdefender’s antimalware and advanced threat intelligence solutions, GravityZone Security for Mobile enables organizations to vet applications, monitor device status, protect against malicious apps, phishing attacks and more to strengthen their overall cybersecurity posture.


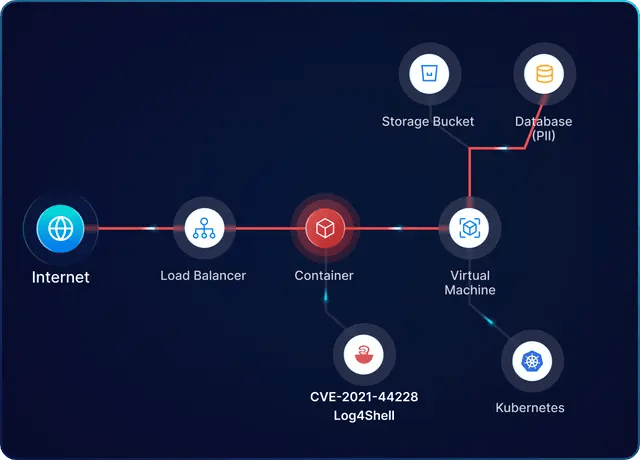
PingSafe helps organizations securely deploy containers with KSPM module
PingSafe launched KSPM module to provide an end-to-end security solution that encompasses the entire container lifecycle, from development to production, helping organizations securely navigate the dynamic landscape of container orchestration.

ConnectSecure enhances its cybersecurity platform with deep attack surface scanning and EPSS
ConnectSecure is adding deep attack surface scanning and the Exploit Prediction Scoring System (EPSS) to its cybersecurity platform for MSPs that protect small and midsize businesses. The new capabilities will be fully integrated into the ConnectSecure platform, giving MSPs complete visibility into network, device, and application weaknesses that can be exploited by bad actors.


CYTRACOM improves efficiency for MSPs with ControlOne platform updates
ControlOne enables MSPs to regain control over their customers’ networks. By eliminating the end user from the equation, MSPs can achieve secure networks and enforce compliance, eliminating vulnerabilities introduced by legacy VPN and on-premises firewalls


Lacework simplifies cloud security with risk calculation on users’ permissions
Lacework announced new CIEM functionality to address the complex and growing challenges in managing identity threats and unnecessary risk within public cloud environments.


Datadog Workflow Automation helps security teams investigate and resolve service disruptions
Datadog released Workflow Automation, a new product that enables teams to automate end-to-end remediation processes—with out-of-the-box actions and pre-built templates—across all systems, apps and services to help identify, investigate and resolve service disruptions and security threats.


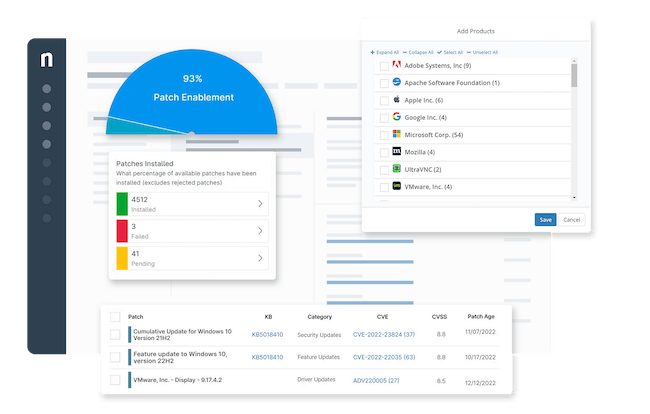
NinjaOne Patch Management enhancements mitigate security vulnerabilities
NinjaOne announced enhancements to NinjaOne Patch Management, delivering the latest automated patching solutions to maintain business operations and keep organizations secure. NinjaOne is simplifying the process with a new patching dashboard, automated Linux and MacOS patching improvements, and patch scheduling flexibility.

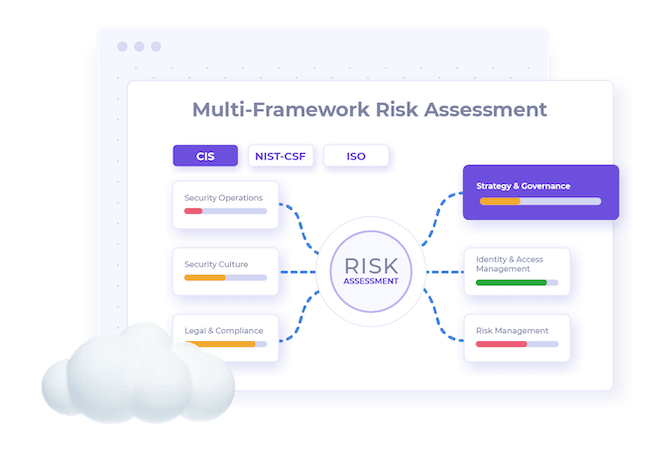
Enveedo Strategy Execution Platform for Security strengthens cyber resiliency for businesses
Enveedo has launched its Strategy Execution Platform for Security that enables organizations to build and maintain cyber resiliency. The platform includes a risk management engine, on-demand access to vCISO guidance, and a real-time centralized view of the organization’s systems, assets, stakeholders, and risks.

1Password introduces two new passkey features to promote passwordless future
Save and sign in with passkeys enables users to create and store passkeys in their 1Password vault, and sign in to their accounts with them through the 1Password beta browser extension. Unlock 1Password with a passkey allows customers to create a new, free 1Password account to preview the passkey login functionality, replacing the need for an account password and secret key combination.


Okta Device Access enables businesses to secure access to both devices and applications
As part of Okta’s Workforce Identity Cloud, Okta Device Access delivers stronger authentication to unlock a device, helping organizations achieve zero trust while simplifying the login experience for employees.


Zilla Security introduces new suite of identity security SaaS solutions
Zilla Security announced Zilla Secure and Segregation of Duties (SOD), two SaaS solutions that enable enterprise-wide identity security for cloud-based applications and infrastructure, SaaS, and legacy applications.


Seceon unveils two products for MSPs and MSSPs to quantify risk
Seceon announced two new products designed to quantify and report on the value of the platform for its partners and their clients. Seceon aiSecurity Score360 service provides comprehensive scanning and risk assessments of attack surfaces, and Seceon aiSecurity BI360 enables partners to select from pre-set compliance and regulatory frameworks, including CMMC, HIPAA, PCI-DSS, NIST, GDPR and perform their own analytics and reporting.


Quantum Origin Onboard strengthens device security against cyberattacks
Quantinuum launched Quantum Origin Onboard, an innovation in cryptographic key generation that provides quantum computing hardened cyber protection for a wide range of connected devices by maximizing the strength of keys generated within the devices themselves.


NETSCOUT introduces Visibility Without Borders platform
NETSCOUT has introduced its Visibility Without Borders platform to help organizations keep goods and services flowing by uniting performance, security, and availability under one common data framework.


iStorage launches datAshur PRO+C with Type-C USB interface
iStorage’s new datAshur PRO+C is a user-friendly USB 3.2 (Gen 1) Type-C flash drive. It employs PIN protection and hardware encryption to safeguard data to military-grade standards. Available in various capacities ranging from 32GB to 512GB, this device is also offered with a USB Type-C to Type-A adapter to ensure users are able to keep pace with the evolving USB interfaces.


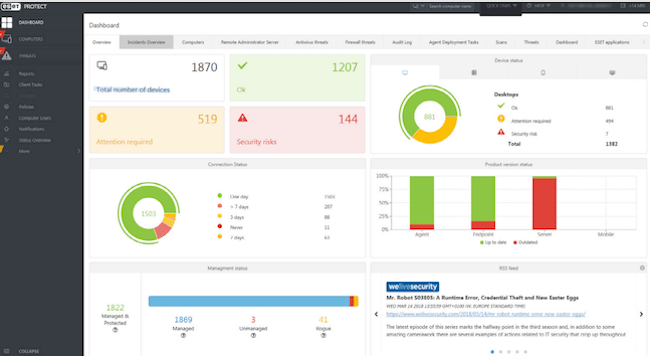
ESET PROTECT Elite defends users against ransomware and zero-day threats
ESET PROTECT Elite delivers enterprises, SMBs, and channel partners with enterprise-grade XDR for increased visibility and threat-hunting capabilities. The comprehensive offering combines multilayered endpoint protection with multi-factor authentication, server security, advanced threat defense, full disk encryption, mail security and cloud application protection.

Cymulate Exposure Analytics provides users with an attacker’s view of their cyber resilience
Rather than simply prioritizing based on CVSS scores, Cymulate Exposure Analytics provides a security data fabric for contextualized vulnerability prioritization, which correlates vulnerability findings with business context and security control effectiveness.


Edgescan EASM allows organizations to secure their critical assets and applications
The Edgescan EASM solution solves the lack of visibility and slow remediation response challenges presented by legacy tools and manual processes. Integrated with Edgescan Penetration Testing as a Service (PTaaS) and Risk-based Vulnerability Management (RBVM) capabilities, EASM provides complete visibility and assessment across multi-cloud and on-premises infrastructures.


Netskope Intelligent SSE helps enterprises securely manage employee use of generative AI apps
Netskope has released a comprehensive data protection solution to help enterprises securely manage employee use of ChatGPT and other generative AI applications, such as Google Bard and Jasper. As part of its Intelligent Security Service Edge (SSE) platform, Netskope enables safe usage of generative AI thanks to patented data protection techniques.


Delinea Privilege Manager enhancements reduce phishing effectiveness
Based on Delinea’s deep expertise and customer feedback, the new Workstation Policy Framework includes five of the most common policies to help customers quickly build a foundation for privileged access controls and create a baseline of security on Windows and Mac workstations without disrupting user productivity.


Index Engines CyberSense 8.3 identifies malicious changes indicative of cyberattack
Index Engines announced CyberSense 8.3, which features several user experience updates highlighted by additional metrics after a ransomware attack is detected, a new setup wizard and system configuration interface.


NetApp BlueXP updates simplify backup and recovery
The new capabilities available through BlueXP deliver data service capabilities that can discover, manage, and protect data across the multicloud infrastructure, leveraging AI/ML operations for optimum business results.


Cequence Security strengthens API protection platform with generative AI and no-code security automation
Cequence Security announced new updates to the Unified API Protection (UAP) platform that strengthen customers’ ability to discover, manage risk and protect APIs. With the latest capabilities, organizations can deploy API Security Testing with built-in generative AI automation, protect users from online fraud and operationalize security findings with low-code/no-code workflows.

Source: https://www.helpnetsecurity.com/2023/07/03/infosec-products-of-the-month-june-2023/
You may like

IoT security threats highlight the need for zero trust principles

New infosec products of the week: October 27, 2023

Raven: Open-source CI/CD pipeline security scanner

Apple news: iLeakage attack, MAC address leakage bug

Hackers earn over $1 million for 58 zero-days at Pwn2Own Toronto







