
Major enterprise software vendors Fortinet, Ivanti, and SAP have released urgent security updates addressing multiple critical vulnerabilities that could enable...














A newly expanded cyber espionage network linked to China-nexus threat actors has grown rapidly in scale and sophistication, with security researchers warning that the “JDY botnet”...

June 10, 2026: Cybersecurity researchers have uncovered six security vulnerabilities in the widely used JavaScript library protobuf.js, warning that the flaws could enable attackers to execute...
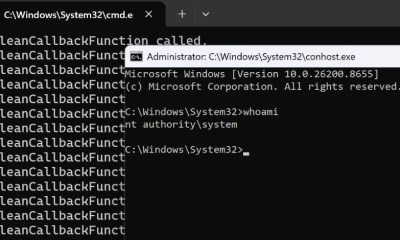

June 10, 2026: A newly disclosed zero-day vulnerability affecting Microsoft Defender has sparked fresh cybersecurity concerns after a security researcher released a proof-of-concept (PoC) exploit capable...


June 9, 2026: Backup and recovery software provider Veeam Software has released urgent security updates to address a critical vulnerability in its Backup & Replication platform...


June 9, 2026: Social media giant Meta Platforms has announced a significant expansion of its personalization framework, revealing plans to use information received from external businesses...


A new cybersecurity investigation has revealed that certain free consumer applications may be quietly transforming smart TVs and other connected devices into residential proxy nodes, allowing...


OpenAI has announced the rollout of a new security-focused feature called Lockdown Mode for ChatGPT, aimed at reducing the risk of sensitive information being exposed through...


Artificial intelligence is rapidly reshaping the cybersecurity landscape, and this week’s developments highlight just how dramatically vulnerability discovery is accelerating. Researchers have revealed that an autonomous...


The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added a newly discovered vulnerability affecting SolarWinds Serv-U file transfer software to its Known Exploited Vulnerabilities (KEV)...


A rapidly evolving software supply chain threat known as Miasma has compromised dozens of Microsoft-hosted GitHub repositories, marking one of the most significant open-source ecosystem attacks...
Recent Comments