

A sophisticated phishing campaign leveraging artificial intelligence (AI) has compromised the Microsoft cloud accounts of hundreds of organizations worldwide, according to cybersecurity researchers at Huntress. The...


This week’s developments reveal a broader shift in the cyber threat landscape. Rather than a single headline-grabbing breach, security researchers tracked a steady stream of attacks...
Security researchers have revealed a newly discovered hardware vulnerability in AMD processors that weakens the protections offered by Secure Encrypted Virtualization with Secure Nested Paging (SEV-SNP),...
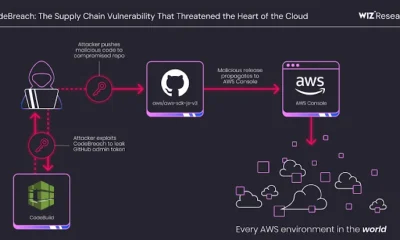

A critical misconfiguration in AWS CodeBuild exposed several high-profile GitHub repositories to potential supply chain attacks, according to cloud security researchers at Wiz. The vulnerability, dubbed...

Even people who are careful online—locking down social media accounts, avoiding suspicious calls, and using strong passwords—may still be exposing far more personal information than they...
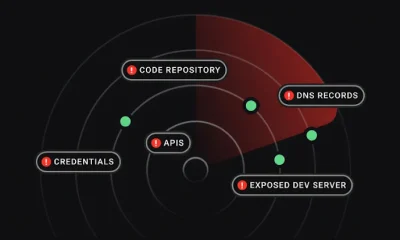

Attack Surface Management (ASM) tools are designed to reduce cyber risk, but many organizations struggle to demonstrate a clear return on investment. While these platforms excel...


Docker has opened access to more than 1,000 hardened container images, making them free and open source for developers worldwide. These images, initially part of Docker’s...