

In the past decade, digital transformation has become a buzzword in nearly every industry. Organizations have scaled down workforces in favor of automation, moved their servers and networks...
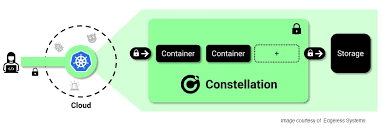

Confidential Computing is a hardware-based technology that shields computer workloads from their environments and keeps data encrypted during processing. In this Help Net Security video, Felix...


We already have cybersecurity behaviors we learned from elsewhere, especially those who have grown up with technology. Initially, cybersecurity starts from home and school, and it...


Google announced today that it’s introducing passkey support to its Chrome web browser and the Android operating system to simplify sign-ins across apps, websites, and devices....


COVID-19-themed phishing messages are once again spiking in the U.S. following a prolonged summer hiatus that appears to be over. According to a report by email...


Security researchers have discovered an npm timing attack that reveals the names of private packages so threat actors can release malicious clones publicly to trick developers...


Aruba has released security updates for the EdgeConnect Enterprise Orchestrator, addressing multiple critical severity vulnerabilities that enable remote attackers to compromise the host. Aruba EdgeConnect Orchestrator...


Microsoft has added command-and-control (C2) traffic detection capabilities to its Microsoft Defender for Endpoint (MDE) enterprise endpoint security platform. Available in public preview at the moment,...


The Information Technology and Innovation Foundation said a U.S.-led forum could develop “a set of voluntary, consensus-based guidelines” for social media platforms to use when moderating...


Old lore held that shooting a werewolf, vampire, or even just your average nasty villain with a silver bullet was a sure-fire takedown: one hit, no...