

Ransomware gangs are planning on trying out a new tactic, and it involves the destruction of the victims’ data. Targeting the data Researchers from Symantec, Cyderes and...


Use these three questions to assess your company’s preparedness to retrieve lost data. 1. Do you have backups of your data? This fundamental question is the...


https://player.vimeo.com/video/751211245?h=58b28871bf&badge=0&autopause=0&player_id=0&app_id=58479&dnt=1 In this Help Net Security video, Joe Leonard, CTO at GuidePoint Security, illustrates how the role of the CIO is changing as cybersecurity priorities and responsibilities...
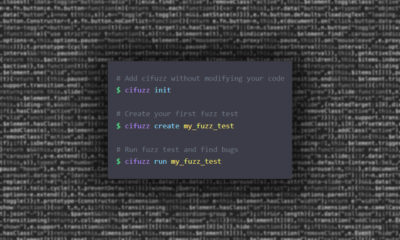

Fuzz testing helps developers protect their applications against memory corruptions, crashes that cause downtime, and other security issues, including DoS and uncaught exceptions. Code Intelligence has...


The APWG’s Phishing Activity Trends Report reveals that in the second quarter of 2022, the APWG observed 1,097,811 total phishing attacks — the worst quarter for phishing that...


SolarWinds unveils the results of its survey examining the state of the technology job market amid industry-wide labor shortages and hiring challenges. Released to coincide with the eighth-annual...


A recently resolved vulnerability in Sophos Firewall has been abused by attackers in targeted attacks, the vendor warns. The critical vulnerability (CVE-2022-3236) poses a remote code execution (RCE) risk. Sophos...


Java templating engine Pebble was vulnerable to a bug that could allow attackers to bypass its security mechanisms and conduct command injection attacks against host servers. Pebble Templates...


The VA’s Office of Inspector General found “critical and high-risk vulnerabilities on 37% of the devices” at the Louisiana-based medical center. An audit conducted by the...


Security researchers have discovered 75 applications on Google Play and another ten on Apple’s App Store engaged in ad fraud. Collectively, they add to 13 million...