

49% of respondents to a recent Twitter poll carried out by Osirium Technologies describe endpoint management security within their organization as non-existent. 11% admit that it’s their lowest...


Campaigners for reform of the UK’s Computer Misuse Act (CMA) have identified cybersecurity activities that should be legally defensible ahead of a government review of the...


Wiz Research has found vulnerabilities in popular ‘PostgreSQL-as-a-Service’ offerings from various cloud vendors, introduced by the cloud vendors themselves. Earlier this year, the security outfit discovered...


CS.MONEY, one of the largest platforms for trading CS:GO skins, has taken its website offline after a cyberattack allowed hackers to loot 20,000 items worth approximately...
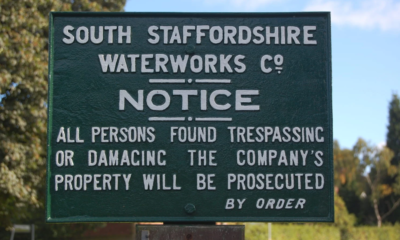

South Staffordshire Water, a company supplying 330 million liters of drinking water to 1.6 consumers daily, has issued a statement confirming IT disruption from a cyberattack....


Argentina’s Judiciary of Córdoba has shut down its IT systems after suffering a ransomware attack, reportedly at the hands of the new ‘Play’ ransomware operation. The...


Monero, the privacy-oriented decentralized cryptocurrency project, underwent a planned hard fork event on Saturday, introducing new features to boost its privacy and security. The network upgrade...


A dozen malicious Python packages were uploaded to the PyPi repository this weekend in a typosquatting attack that performs DDoS attacks on a Counter-Strike 1.6 server....


Phone numbers of close to 1,900 Signal users were exposed in the data breach Twilio cloud communications company suffered at the beginning of the month. Twilio...


The Microsoft Threat Intelligence Center (MSTIC) has disrupted a hacking and social engineering operation linked to a Russian threat actor tracked as SEABORGIUM that targets people...