
A new malware family has been discovered that uses Common Log File System (CLFS) to stay undetected. Named PRIVATELOG, this malware uses another malware—StashLog—as its installer. What’s...


The Jenkins project says it has fallen prey to widespread attacks targeting a critical vulnerability in Confluence, Atlassian’s team collaboration software. Attackers compromised Jenkins’ deprecated Confluence...


The Securities and Exchange Commission (SEC) has sanctioned eight financial services firms for cybersecurity failures that resulted in email account takeovers exposing the personal information of...


Hackers have released proof-of-concept code that exploits a recently demonstrated vulnerability in older but still widely used versions of Ghostscript, the popular server-side image conversion software package. Security...


The United States Department of Homeland Security (DHS) has announced two senior cybersecurity appointments. Former lead solution engineer at Salesforce, David Larrimore, has been named the DHS’s Chief...


Pixalate, a firm that provides fraud protection for mobile app and connected TV (CTV) advertising, has raised $18.1 million in growth capital, bringing the total amount...


The vast amount of data constantly collected by the billions of sensors and devices that make up the IoT can pose a serious processing challenge for businesses that...


In the 12th Century, Mongols successfully raided walled cities, one after the other, leading to the demise of walled-city architecture for protection. In our modern 21st...


Hackers are entrepreneurs. After legitimate developers built software-as-a-service (SaaS) businesses by renting access to productivity software, cybercriminals seeking new revenue streams created malware-as-a-service (MaaS) as a...
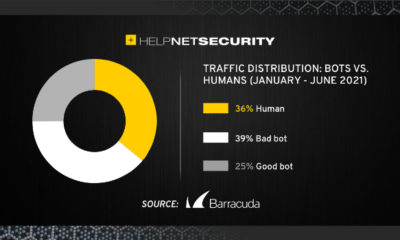

Automated traffic takes up 64% of internet traffic – and whilst just 25% of automated traffic was made up by good bots, such as search engine...