

Organizations are being urged to rethink cybersecurity defense strategies as traditional patch-and-protect models struggle to keep up with rapidly evolving threats, including AI-driven exploits and persistent...


A sophisticated software supply chain attack has compromised multiple Red Hat-associated npm packages, allowing attackers to steal sensitive credentials, infect developer environments, and potentially spread malware...

SAN FRANCISCO — Password management platform Dashlane has disclosed a cybersecurity incident in which attackers successfully downloaded encrypted password vaults from a small number of customer...


A rapidly emerging cybersecurity risk is coming from an unexpected source: employees independently building full-scale applications using AI-powered “vibe coding” platforms and deploying them directly to...
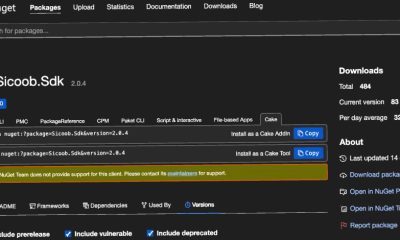

Cybersecurity researchers have uncovered a coordinated wave of software supply chain attacks involving malicious packages published to both NuGet and npm registries, designed to steal sensitive...


Advanced Phishing, SEO Poisoning, and Fake Software Installers Used to Spread MiniFast and MiniJunk V2 A state-linked Iranian cyber espionage group identified as Nimbus Manticore, also...


Drupal has released urgent security updates to address a highly critical vulnerability that could allow attackers to execute malicious code, escalate privileges, or access sensitive information...


GitHub has confirmed that a recent breach of its internal repositories was caused by a compromised employee device infected through a malicious version of the popular...


Microsoft has dismantled a large-scale malware-signing-as-a-service (MSaaS) operation allegedly used to distribute ransomware and other malicious software under the guise of legitimate applications. The disruption, carried...


Microsoft has released two new open-source tools—RAMPART and Clarity—aimed at improving how developers design, test, and secure AI agents throughout the development lifecycle. The announcement marks...
Recent Comments