

The term “deepfake” is used for photo, video or audio content that has been manipulated to make it seem that the subject is doing or saying...


A car theft ring that used fraudulent software to “hack” and steal vehicles with remote keyless entry and ignition systems has been dismantled by the French...


As schools have become more digital, they’ve taken a somewhat backward approach to cybersecurity, historically moving slowly, and have weak cybersecurity controls and protocols. In this...

Trellix released global research revealing the cost of siloed security, weak spots in protection, and lack of confidence amongst security operations teams. This Help Net Security video...


Kylie Wright-Ford was recently named CEO of RSA Conference LLC. She joins RSAC with an extensive track record of building communities for business professionals, having served in...


Forescout’s research team analyzed 19 million connected devices deployed across five different industries, to find the riskiest device groups: smart buildings, medical devices, networking equipment, and...


Cybersecurity measures are increasingly failing to close gaps, and the healthcare industry, in particular, has become a high-dollar target due to limited budgets and quick ransom pay-offs....


The managed IT services market is growing both in size and importance, as more organizations decide it makes fiscal and operational sense to outsource key functions....
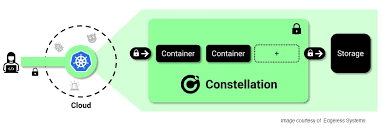

Confidential Computing is a hardware-based technology that shields computer workloads from their environments and keeps data encrypted during processing. In this Help Net Security video, Felix...


We already have cybersecurity behaviors we learned from elsewhere, especially those who have grown up with technology. Initially, cybersecurity starts from home and school, and it...
Recent Comments