

Kylie Wright-Ford was recently named CEO of RSA Conference LLC. She joins RSAC with an extensive track record of building communities for business professionals, having served in...


Forescout’s research team analyzed 19 million connected devices deployed across five different industries, to find the riskiest device groups: smart buildings, medical devices, networking equipment, and...


Cybersecurity measures are increasingly failing to close gaps, and the healthcare industry, in particular, has become a high-dollar target due to limited budgets and quick ransom pay-offs....


The managed IT services market is growing both in size and importance, as more organizations decide it makes fiscal and operational sense to outsource key functions....
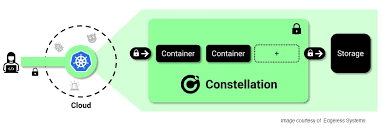

Confidential Computing is a hardware-based technology that shields computer workloads from their environments and keeps data encrypted during processing. In this Help Net Security video, Felix...


We already have cybersecurity behaviors we learned from elsewhere, especially those who have grown up with technology. Initially, cybersecurity starts from home and school, and it...


Old lore held that shooting a werewolf, vampire, or even just your average nasty villain with a silver bullet was a sure-fire takedown: one hit, no...


In the past few months, we’ve seen an unprecedented number of identity theft attacks targeting accounts protected by two-factor authentication (2FA), challenging the perception that existing...


Proofpoint released their Cybersecurity: The 2022 Board Perspective report, which explores board of directors’ perceptions about their key challenges and risks. Cybersecurity is dominant on their agendas. Seventy-seven...


Oxeye researchers discovered a severe vm2 vulnerability (CVE-2022-36067) that has received the maximum CVSS score of 10.0. Called SandBreak, this new vulnerability requires R&D leaders, AppSec...
Recent Comments